Click on any item below for an in-depth overview.
Case Study: AMD (Advanced Micro Devices)
Securing the Future of High-Performance Computing: Glog.AI & AMD ROCm™
The Partner AMD is a global leader in high-performance computing, graphics, and visualization technologies. Their ROCm™ (Radeon Open Compute) platform is a pivotal open-source stack for GPU computing, powering some of the world’s most advanced AI and research workloads.
The Challenge Open-source ecosystems of this scale present a massive attack surface. AMD required a way to systematically evaluate the security posture of the entire ROCm™ organization on GitHub comprising hundreds of individual repositories as well as the critical AMDGPU Linux driver integrated into the Linux kernel (v6.16).
The Solution: Automated Intelligence at Scale Glog.AI deployed its automated security scanning engine to provide deep visibility into these mission-critical projects.
-
Massive Scale Scanning: Automated security configurations were established for all 343 repositories within the AMD ROCm™ organization.
-
Kernel-Level Analysis: Targeted analysis of the AMDGPU driver within the 6.16 kernel, ensuring the foundation of GPU-OS interaction remains resilient.
-
Software Product Inventory (SPI): All data was funneled into Glog.AI’s centralized dashboard, a “single pane of glass” that provides real-time inventory, security data, and vulnerability analysis.
The Results By transitioning from manual oversight to an automated, centralized model, Glog.AI provided AMD with:
-
Comprehensive Visibility: A complete security map of 343 repositories.
-
Centralized Management: The ability to track vulnerabilities across disparate projects through the Glog.AI SPI dashboard.
-
Proactive Remediation: Faster identification of potential risks within the ROCm™ stack and Linux kernel drivers.
Key Highlights
- Massive Scale: Scanned 343 repositories and provided comprehensive, actionable remediation advice.
- Centralized Management: Established a centralized inventory and management system for all software products.
- Seamless Integration: Automated security processes through direct GitHub workflow integration.
- Actionable Insights: Delivered highly accurate, context-specific remediation advice directly to developers.
- Enhanced Accuracy: Significantly reduced false positives, filtering out the noise to focus exclusively on true vulnerabilities.
- Drastic Time Savings: Eliminated thousands of hours typically spent manually analyzing and triaging security findings.
- Operational Efficiency: Streamlined the vulnerability resolution process without slowing down agile delivery schedules.
- Proactive Security: Empowered the team to adopt a “security by design” approach right at the source code level.
Articles
Discover how Glog.AI enhances cybersecurity and software security. Our articles delve into real-world examples and explain the ‘how’ behind our solutions.
- How Glog.AI Products, Solutions, and Services Enhance Security for Telecom Businesses
- Glog.AI Helped Easy Aerial Achieve Blue UAS Cleared List Inclusion
- Glog.AI Products & Services Matrix
- Is Your Software Secure Enough for the Evolving Threat Landscape?
- Glog.AI comprehensive and proactive approach to building secure software
- Glog.AI Application Security Management (GASM) product helps Application Security Posture Management (ASPM)
- Use Glog.AI Solution to Make Software More Secure at High Technology Company
- Why would you recommend using Glog.AI products to software companies?
- Glog.AI and GitHub Integration
- Glog.AI makes payment systems more secure and resistant to hacker attacks
- Glog.AI makes online stores more secure
- Glog.AI: Transforming Software Security for a Leading Fintech Innovator
- Glog.AI helps secure critical infrastructure
- Glog.AI helps gaming software security and compliance as mandated by WLA Security Control Standard
- Glog.AI helps security checks, audits and remediation in blockchain based systems
- Glog.AI helps automotive and autonomous driving
- How does Glog.AI give peace of mind to software development, security and compliance teams?
- Security in Software Product and Application Development
- Glog.AI and EU Product Liability Directive
- Threat-Driven Static Application Security Testing (SAST)
- Glog.AI helps to be compliant with security standards and regulations
- Glog.AI helps startups
- Reduce costs and increase security by using the Glog.AI solution
- Glog.AI – a valuable asset for your software development department
- The Return on Investment (ROI) for Glog.AI
- Significant cost savings for businesses by using Glog.AI
- Glog.AI helps StateRAMP
- An example of a successful integration with Glog.AI
- Glog.AI helps software outsourcing companies develop more secure code
- Importance of software code security for banks and financial institutions
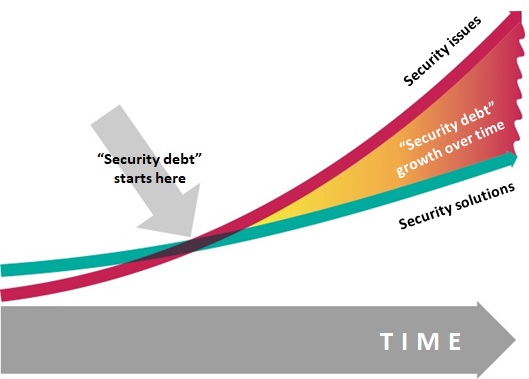
- Why do companies that develop and sell software not take enough care of security flaws?
- Why do companies not prefer to invest in software security solutions?
- How Glog.AI can help to implement Agile process in software development?
- How does application security protect against ransomware?
- How Glog.AI can help remediation of software security vulnerabilities?
- GenAI code generators and software security
- Geneva Manual recommends Glog.AI
- Security of code generated by GitHub Copilot and how to fix it with Glog.AI
Glog.AI Products & Services Matrix
| Product/Service Name | Core Functionality | Key AI/ML Differentiators | Target Use Case |
|---|---|---|---|
| Glog.AI – Software Security | Automated code vulnerability identification and remediation during development | AI-powered contextual analysis, automated fixing, false positive reduction | DevSecOps, Application Security |
| NetEcho – Network Security | Predictive network and endpoint threat detection, anomaly identification | AI-driven behavioral analysis, threat forecasting | Network Security Monitoring, Endpoint Protection |
| Security Predictions | Anticipation of emerging attack patterns and potential targets | Advanced AI analysis of diverse threat intelligence feeds, proprietary prediction algorithms | Proactive Threat Intelligence, Strategic Security Planning |
| vSOC | Virtual Security Operations Center services | Leverages NetEcho & Security Predictions, AI-assisted analysis by human experts | Continuous Security Monitoring, Incident Response |
| Penetration Testing | AI-enhanced vulnerability identification and assessment | More efficient, comprehensive, and insightful analysis through AI assistance | Security Audits, Vulnerability Management |
| Trainings | Secure software development education | Practical, up-to-date secure coding practices | Developer Upskilling, Building Security Culture |
This matrix provides a structured overview of Glog.AI’s portfolio, highlighting the AI-centric nature and specific value proposition of each offering.
Case Study: EuroICC
EUROICC is hardware and software manufacturer, R&D outsourcing partner and system integrator in automation. Smart Hotel Control products enable our business partners to work more efficiently, safely and cost effectively. Its ToCCata guest room management system incorporates room monitoring and hotel management.
Business Challenge
Guest Room Management System based on C series of micro-controllers is a flexible solution applicable for different size hotels – from small inns to luxurious hotels. Main functionalities are access control, power saving, staff monitoring and more effective processing of different alarms, requiring EuroICC to consistently meet the highest levels of data security and safety. The main challenge is to reduce risk and secure EuroICC’s software products throughout the Software Development Lifecycle (SDLC) without slowing down delivery schedules. It is also required from EuroICC to meet business needs to deliver new, updated, or customized products to market as quickly as possible. EuroICC’s goal was to make software secure at the source code level and incorporate security focused culture into SDLC from the ground as a single security breach could seriously harm the company and its customers. EuroICC team lead said: “Our software operates on the hotel network and also communicates with different internal and external software and services such as BMS, PMS, CMS and ACS. Software works in an environment which can be threatened and attacked from different points and, as part of the hotel network, it must fulfill the highest security standards in order to be a reliable part of the whole system. Thus, we came up with the idea of using Glog which should help us find real security threats potentially missed in development and remediate them efficiently. Same time, an important outcome is increasing the ability of our engineers to improve software architecture in terms of security.”
Results
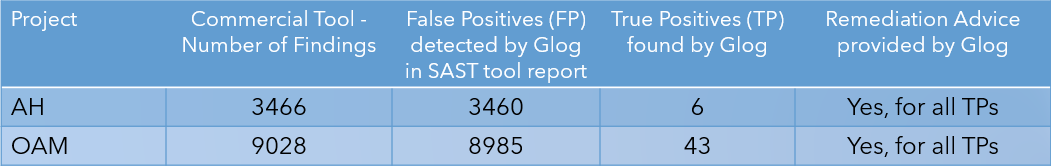
Glog team provided services to secure software on source code level, saved scanning time and improved scan coverage of source code providing only relevant scan results to EuroICC developers. Trustworthy scan results without false positive findings and in-context remediation advice, helped developers in their effort to increase software’s security. Glog provided the possibility to detect potential security vulnerabilities, remediate within required timeframes and deliver more secure software products. It saves days of developers’ work usually needed to scan, triage and fix findings in their source code. Glog solution helped EuroICC to be proactive in discovering and fixing security issues. Additionally, EuroICC was able to implement security by design approach to make software more secure. EuroICC team lead continued: “Firstly, we got clear analysis about security weaknesses of our software product. With detailed explanation of the nature of the issues and clear remediation advice by Glog, our developers are able to fix the code with vulnerabilities and make it more secure. Overall, we saved a tremendous amount of time and energy on finding and analyzing the threats, triaging it including prioritization, and then remediation and fixing the security vulnerabilities. Finally, the experience working with the Glog team is valuable for our future development and maintenance of our software.”
About Glog
Glog project is focused on research and development of a solution which gives remediation advice for security vulnerabilities in software code based on context. Moreover, it is capable of automatically fixing those vulnerabilities. We are developing such a solution based on machine learning and AI. Agility in software security is becoming a reality! More info at www.glog.ai.
False Positives Challenge
General use cases
Select your scenario to see how we can help:
Software Development Company
Startup
Software User
Regulatory Body
Compliance
Feel free to contact us for help.