In an era of relentless and sophisticated cyber threats, traditional security approaches are no longer sufficient. Glog.AI emerges as a beacon of innovation, offering a comprehensive, AI-driven cybersecurity ecosystem designed to not only react but to anticipate and proactively neutralize risks.
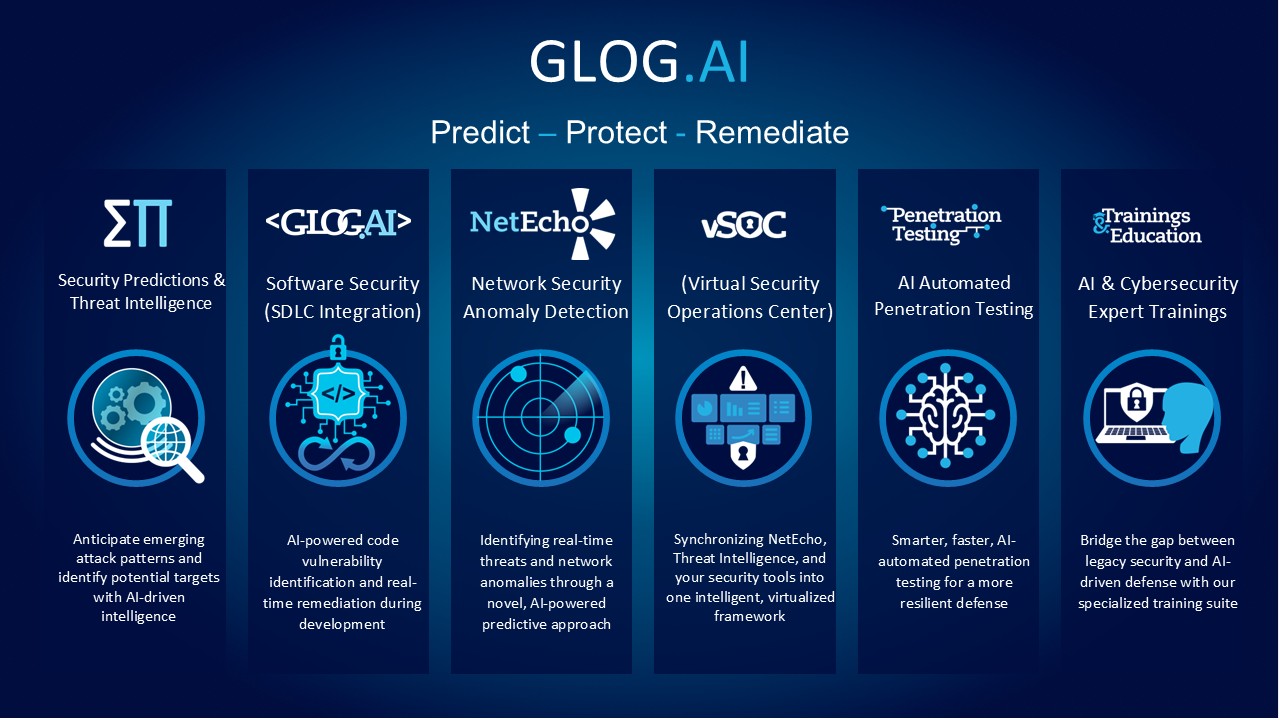
This article delves into the core components and pioneering spirit of Glog.AI, leveraging the overview provided in our central visual diagram, which illustrates our holistic approach across six key domains: Threat Intelligence, Software Security, Network Anomaly Detection (NetEcho), the Virtual Security Operations Center (vSOC), Automated Penetration Testing, and Expert Trainings.
A Comprehensive View of the Glog.AI Ecosystem
Glog.AI’s mission is succinctly captured in our core operating philosophy: Predict, Protect, Remediate. We move beyond siloed solutions, providing an integrated framework where intelligence flows seamlessly across the security infrastructure.
As illustrated in our visual overview, Glog.AI provides a 360-degree approach that covers every stage of the security lifecycle. Here’s a detailed look at how each component operates within this powerful framework.
1. The Power of Foresight: Security Predictions & Threat Intelligence
The foundation of Glog.AI’s predictive capability lies in our Security Predictions & Threat Intelligence module. Rather than simply reacting to known threats, we leverage advanced AI to analyze emerging attack patterns globally.
- Anticipate Emerging Attack Patterns: Our AI models ingest massive datasets to forecast potential attacks before they happen.
- Identify Potential Targets: By recognizing shifts in adversary behaviors, we provide actionable intelligence that allows organizations to harden their defenses proactively.
2. Securing the Core: Software Security with SDLC Integration
Security must start at the foundation of code. Glog.AI Software Security integrates directly into the Software Development Life Cycle (SDLC), making “Security by Design” a reality.
- AI-Powered Code Vulnerability Identification: Our AI systems scan code repositories in real-time, detecting potential vulnerabilities far earlier and more accurately than traditional static analysis tools.
- Real-Time Remediation During Development: We empower developers with immediate insights and automated remediation suggestions, reducing the cost and complexity of patching security flaws post-deployment.
3. NetEcho: Network Security Anomaly Detection
For real-time visibility and defense against network threats, Glog.AI introduces NetEcho. This solution provides an intelligent, automated way to monitor and secure network infrastructure.
- Identifying Real-Time Threats: NetEcho identifies threats as they evolve, rather than relying solely on outdated signature-based detection.
- Novel AI-Powered Predictive Approach: By baselining normal network activity and using predictive algorithms, NetEcho detects anomalies that signify a potential breach, insider threat, or lateral movement, enabling immediate response.
4. vSOC: The Virtualized Nerve Center for Security
Managing disparate security tools is a significant challenge for modern security teams. Glog.AI’s vSOC (Virtual Security Operations Center) offers a unified, intelligent command center.
- Synchronizing Intelligence: vSOC aggregates data from NetEcho, Threat Intelligence feeds, and an organization’s existing security stack.
- One Intelligent, Virtualized Framework: By providing a single pane of glass enhanced by AI, vSOC streamlines operations, improves visibility, reduces alert fatigue, and enables faster, more coordinated incident response.
5. AI Automated Penetration Testing: Continuous Resilience Validation
Manual penetration testing is too slow and infrequent for today’s dynamic threat environment. Glog.AI automates this critical function with AI Automated Penetration Testing.
- Smarter, Faster Testing: Our AI agents conduct multi-stage attacks at scale, finding complex vulnerabilities that traditional scanners miss.
- More Resilient Defense: By moving to a continuous validation model, organizations gain persistent visibility into their security posture, ensuring their defenses remain resilient even as their infrastructure changes.
6. Bridging the Gap: Trainings & Education
Acknowledging that cybersecurity is a human-centric challenge, Glog.AI invests heavily in the next generation of defenders through our Trainings & Education division.
- AI & Cybersecurity Expert Trainings: We offer specialized courses designed by industry practitioners.
- Specialized Training Suite: Our suite bridges the gap between traditional security practices and the new, AI-driven defense paradigm, ensuring teams have the skills needed to effectively utilize, manage, and understand AI in a security context.
Glog.AI: Market Adoption and Industry Recognition
The Glog.AI integrated approach, fusing predictive AI with autonomous remediation, has resonated strongly across the cybersecurity landscape. Founded by globally recognized experts, the company has seen rapid adoption within high-stakes sectors, including Finance, Telecom, Gaming, and Aerospace & Defense. Our footprint now extends across Government, Critical Infrastructure, and Healthcare, proving that Glog.AI’s methodology is the new standard for mission-critical security.
Our commitment to innovation has not gone unnoticed. Glog.AI is proud to have received numerous industry accolades, awards for innovation in AI security, and frequent features in leading technology and security publications. This industry recognition underscores Glog.AI’s leadership in defining the future of automated security.
Conclusion
Glog.AI is more than a security provider; it is a visionary partner in securing the digital future. By uniting the pillars of prediction, protection, and remediation into a cohesive, AI-driven ecosystem, we empower organizations to move beyond reactive defense to a posture of confident, autonomous security. As visualised in our framework, Glog.AI delivers a future where critical systems are safeguarded by the intelligent, continuous, and integrated defense they require.